10 Best Security Testing Tools Shortlist
Here's my pick of the 10 best software from the 20 tools reviewed.
Our one-on-one guidance will help you find the perfect fit.
You want to evaluate and improve the security of your software systems, networks, and applications and need the right tool for your projects and team. I've got you covered!
In this post, I share my personal experience using dozens of different security testing software with various teams and my picks of the best security testing tools.
What Are Security Testing Tools?
Security testing tools are software used to assess and improve the security of computer systems, networks, mobile devices, and applications. These tools perform various tasks such as identifying vulnerabilities, simulating cyber-attacks, analyzing code for security flaws, and ensuring compliance with security standards. They play a crucial role in the proactive detection and mitigation of potential security threats.
The benefits and uses of security testing tools include enhancing the overall security posture of digital environments, protecting against unauthorized access and data breaches. They help in identifying and addressing security vulnerabilities early, reducing the risk of cyber-attacks. By ensuring compliance with security regulations, these tools build trust and credibility among users and stakeholders. They are essential in today’s digital landscape, where maintaining robust security practices is vital for protecting sensitive information and systems.
Best Security Testing Tool Reviews
Here’s a brief description of each security testing tool to showcase their best use case, some noteworthy features, and screenshots to give a snapshot of the user interface.
Invicti is an enterprise black-box security scanner for identifying vulnerabilities in web applications, websites, and web services. The platform combines dynamic (DAST) and true interactive (IAST) scanning to provide extensive vulnerability coverage and precise threat detection. After vulnerabilities are found, your team can utilize Invicti’s integrations with issue tracking systems to assign them for remediation.
Invicti produces detailed scan reports that enable developers to fix vulnerabilities quickly. Scan reports include various details about each security vulnerability, including its type, variant, classification (i.e., OWASP), location, and potential impact. Reports also include immediate actions developers can take to fix vulnerabilities.
The platform offers over 50 integrations, with support available for GitHub, Jenkins, and Jira.
Vega is a Java based security testing tool that helps you identify vulnerabilities in your applications by finding and validating SQL injection, cross-site scripting and inadvertently disclosed sensitive information. The tool runs on Linux, Mac and Windows, and provides an automated scanner for quick tests and intercepting proxy. Vega is GUI based and is extensible, allowing you to create new attack modules using the API exposed by the app. Vega offers features whereby it can automatically log into sites when supplied with user credentials, and also provides a crawler that powers its automated scanner. The tool also probes for TLS/SSL security settings, allowing you to identify opportunities for improving the security of your TLS servers. Lastly, you can configure Vega’s proxy to run attack modules while you are browsing the target site through it. Vega is fully open source and free to use.
Wapiti is a free security scanner that allows users to audit websites and applications for vulnerabilities. The tool performs black-box scans, meaning it doesn’t study the source code of a web page. It crawls the pages of web applications, attacking scripts and injecting payloads to determine if vulnerabilities are present.
The scanner can detect various vulnerabilities, including SQL and XPath injections, open redirects, and subdomain takeovers. The system can also detect cross-site scripting (XSS) and differentiate between permanent and reflected XSS vulnerabilities. After each scan, Wapiti generates vulnerability reports available for download in various formats, including HTML, XML, and CSV.
SonarQube continuously inspects code quality utilizing static code analysis. The platform generates detailed reports on bugs, code smells, vulnerabilities, and code duplications, enabling software teams to detect security issues early in development. The program supports over 25 programming languages, including Python, Java, C#, and VB.NET.
Developers can ensure their code is ready for release with SonarQube’s Quality Gates, which enforce your organization’s quality policy. Developers can define a set of conditions a project must meet, and SonarQube will indicate whether your code has passed or failed. SonarQube recommends utilizing their default “Sonar way” Quality Gate, which focuses on keeping new code clean and spending less effort remediating old code.
SonarQube integrates with Jenkins, Azure DevOps, BitBucket, GitHub, and many other DevOps platforms.
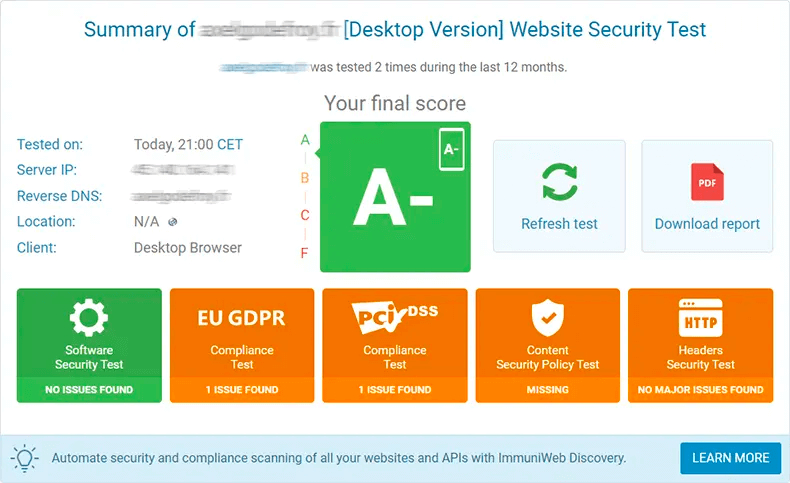
The ImmuniWeb AI Platform offers a variety of SaaS products for asset discovery, penetration testing, and continuous web and mobile application monitoring. Security teams can monitor OWASP Top 10 and SANS Top 25 security vulnerabilities. Immuniweb offers a money-back guarantee if you find any false positives in your vulnerability reports.
ImmuniWeb On-Demand is a great tool to help businesses meet regulatory and compliance requirements in a simple, cost-effective way. It works by regularly performing a penetration test on systems that store or process personal data and identifying privacy misconfigurations that may violate compliance requirements. The platform covers a range of regulations, including HIPPA, California CCPA, CPRA, PCI DSS, Hong Kong PDPO, and EU and UK GDPR.
Users can easily integrate ImmuniWeb products with their existing development, web application firewall, and SIEM tools, including Bugzilla, Azure DevOps, Qualys WAF, and Splunk.
Snyk is a developer-first security platform that automatically identifies vulnerabilities in code, open-source dependencies, containers, and infrastructure as code. Built on an industry-leading security intelligence database, Snky empowers its users to detect more vulnerabilities faster. The platform also supports various programming languages, including JavaScript, Java (Grable, Maven), .Net, Python, and Ruby.
Developers can implement real-time semantic code analysis into development with Snyk’s static application security testing platform, Snyk Code. Powered by machine learning, Snyk Code utilizes logic programming rules to identify security issues as code is written. The system is trained on Snyk’s Vulnerability Database, resulting in fewer false positives.
Snyk integrates with leading DevOps tools, including Microsoft Visual Studio, GitHub, CircleCI, and Jira.
SQLMap is a python-based penetration testing tool that automates the detection and exploitation of SQL injection flaws and database takeovers. Penetration testers can utilize five SQL injection techniques: boolean-based blind, time-based blind, error-based, UNION query, and stacked queries. The system supports MySQL, Oracle, PostgreSQL, IBM DB2, and various other database management systems.
Once SQLMap detects SQL injection bugs in an application, testers can perform extensive database fingerprinting and execute various attacks. Supported attacks include brute-forcing table and column names, dumping database schemas, and enumerating users, privileges, and password hashes.
Penetration testers can integrate SQLMap with Burp Suite, an application testing tool, by utilizing PortSwigger’s SQLiPy extension.
Extensible penetration testing tool with customizable heads up display
OWASP ZAP is a free, open-source penetration testing tool for web applications. The system supports automated and manual penetration testing. ZAP’s ease of use makes the tool accessible to users of all skill levels, from developers to security experts. Testers can utilize ZAP as a stand-alone application or daemon process. Versions of Zap are available for major operating systems and Docker.
Many web application security testing tools aren’t user-friendly; however, ZAP simplifies penetration testing with its intuitive heads up display (HUD). The HUD is a user interface overlaid on a target application, enabling you to access ZAP functionality from any modern browser. This feature is handy for developers, who can efficiently conduct testing on custom build scripts by connecting them to the HUD.
The ZAP Marketplace contains an extensive library of add-ons to extend the tool’s functionality. Add-ons are available for crawling JavaScript-heavy websites and endpoint detection.
BeEF is a security testing tool that focuses on web browser testing. The tool provides extensive cyber security by offering the ability to assess the security posture of your desired environments by using client-side attack vectors. BeEF also uses GitHub to track issues and host its repositories. BeEF aims to look past the hardened network perimeter and client system, allowing you to examine the exploitability within your web browser. The tool hooks one or more browsers, and uses them as front lines for launching further attacks against your systems from within your browser context. BeEF is easy to set up and therefore easy to implement within your workflows. BeEF is fully open source and free to use.
Sonatype offers a suite of products that enable secure software supply chain management. Products include firewalls, application lifecycle management, auditing solutions, repository management, and security tools. Nexus Lifecycle is one of Sonatype’s security tools that helps developers protect their open-source dependencies. The tool automatically identifies and remediates open-source vulnerabilities, allowing enterprise developers to scale open source monitoring across their software supply chain.
Nexus Lifecycle provides a flexible policy engine that gives application security teams complete control of their software. AppSec teams can create custom policies based on app type and organization. Users can also configure policies to report risks to stakeholders or fail software builds based on the severity of policy violations.
Sonatype’s products integrate with popular development tools, including Docker, OpenShift, and Azure DevOps.
The 10 Best Security Testing Tools Summary
| Tools | Price | |
|---|---|---|
| Invicti | Pricing available upon request | Website |
| Vega | No price details | Website |
| Wapiti | No price details | Website |
| SonarQube | From $20,000/year | Website |
| ImmuniWeb | From $499/month | Website |
| Snyk | $98/developer/month | Website |
| SQLMap | Free and open source. | Website |
| Zed Attack Proxy (ZAP) | Free to use | Website |
| BeEF (Browser Exploitation Framework) | No price details | Website |
| Sonatype | From $135/month for 25 developers. | Website |
Compare Software Specs Side by Side
Use our comparison chart to review and evaluate software specs side-by-side.
Compare SoftwareOther Security Testing Tools To Consider
Here are a few more security testing tools that didn’t make the top list.
Comparison Criteria
These criteria will help you evaluate the top security testing tools on the market.
- User Interface (UI): An easy-to-use interface leads to faster adoption of new security testing tools.
- Usability: Developers are increasingly prioritizing security, meaning your testing tools need to be accessible to stakeholders outside the security team.
- Integrations: A security testing tool that supports your existing SIEM and DevOps tools won’t disrupt productivity.
- Value for $: Ensure the cost of your security tool is aligned with the value it provides to keep your IT infrastructure safe.
Security Testing Tools: Key Features
- Asset detection: Automated asset detection ensures your entire IT environment is monitored for critical vulnerabilities.
- Static application security testing (SAST): SAST tools help developers implement security operations earlier in the software development lifecycle.
- Policy management: A flexible policy management system enables DevSecOps teams to enforce software quality standards during each stage of development.
- Threat prioritization: With automated threat prioritization, teams can focus on remediating issues that leave their systems the most vulnerable.
What Do You Think About This List?
Check out more software testing tools on our website and subscribe to our newsletter for the latest insights.